OneLogin Single Sign-On
Configure Pritunl Zero single sign-on with OneLogin
Pritunl Zero supports single sign-on with OneLogin and secondary authentication with OneLogin Protect. SAML attributes will be used to assign roles to the user.
Create Pritunl App on OneLogin
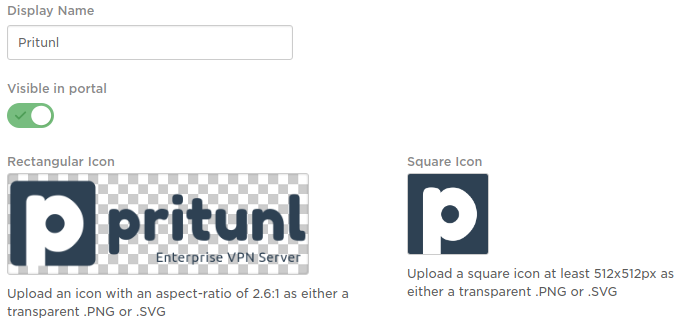
In the OneLogin admin interface select New App and search for SAML Test Connector (IdP w/ attr w/ sign response). Then change the name to Pritunl and download the OneLogin Pritunl logos pritunl.com/img/pritunl_onelogin.png and pritunl.com/img/pritunl_onelogin_square.png. Then upload both logos and click Save.
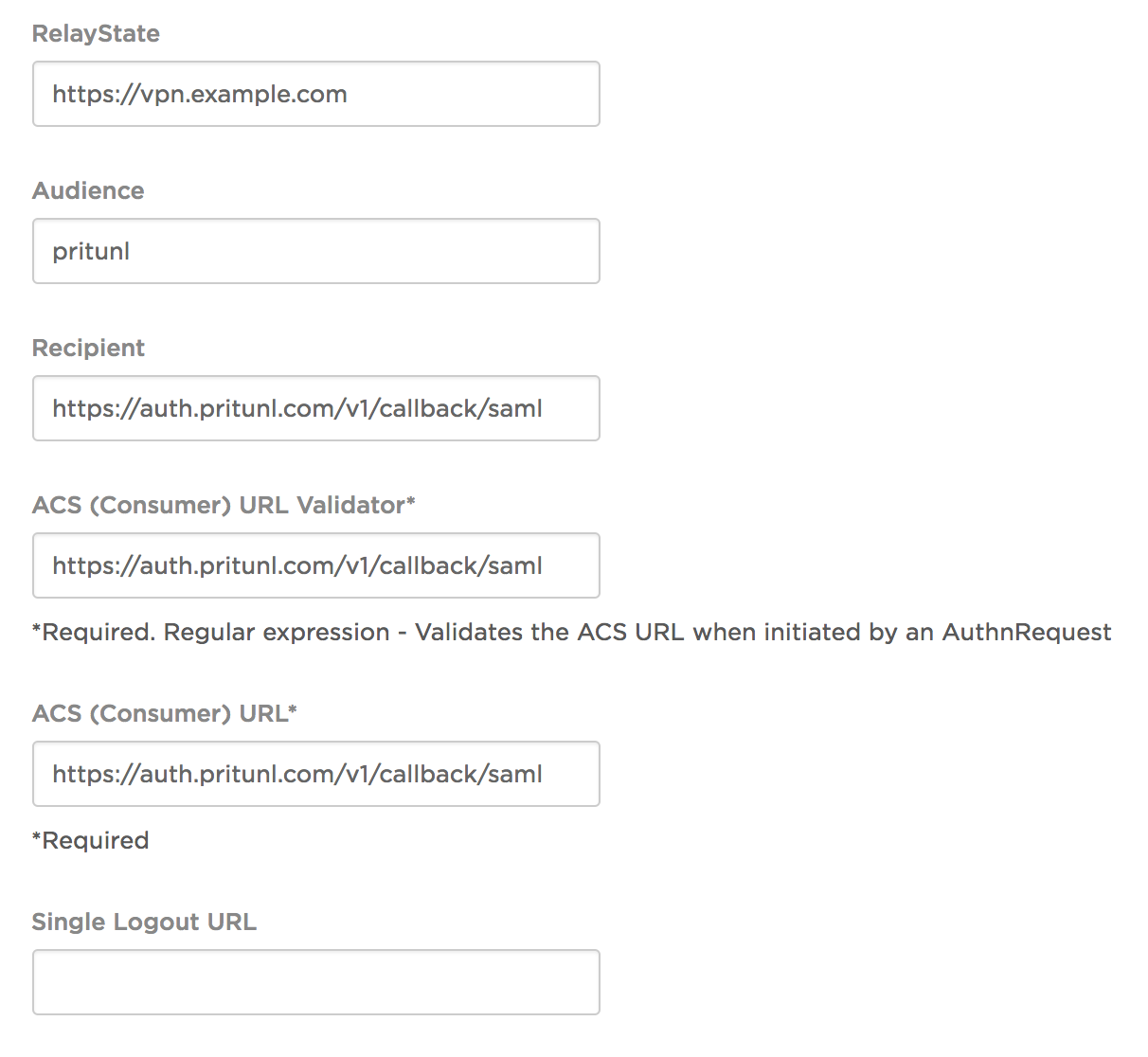
On the next page set the RelayState to the address your users would use to access the Pritunl server such as https://vpn.example.com. Set the Audience to pritunl. Then enter https://auth.pritunl.com/v1/callback/saml as the Recipient, ACS (Consumer) URL Validator and ACS (Consumer) URL. Once done click Save and click the Parameters tab.
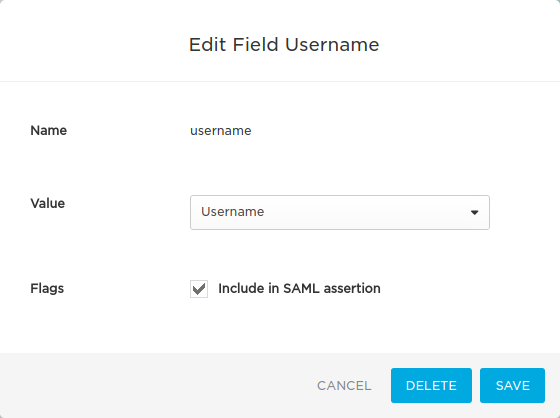
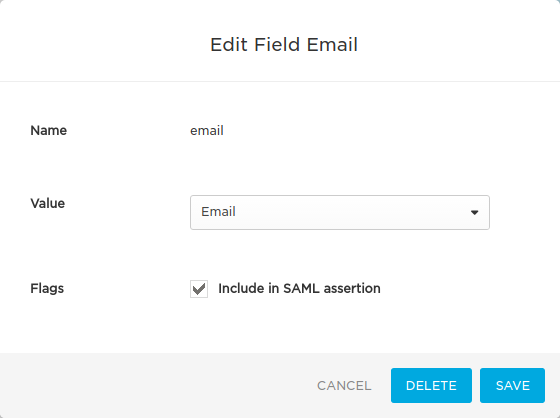
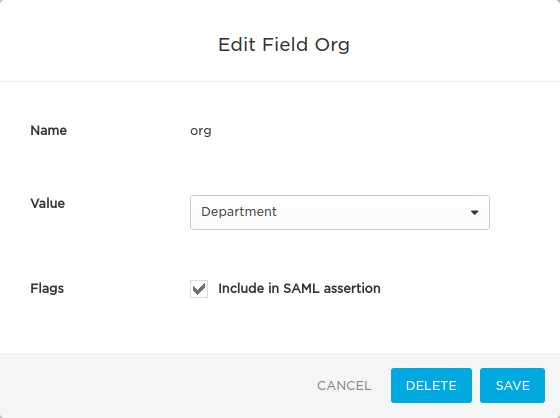
On the parameters tab click Add parameter and set the Field name to username and select Include in SAML assertion then click Save. Then click on the parameter and set the Value to Username. Do this again using email as the name and Email as the value.
Setting User Roles
User roles can be set using the roles attribute. This attribute can be mapped to a value such as Department. Refer to the OneLogin documentation for setting the value of the roles attribute.
Create API Token
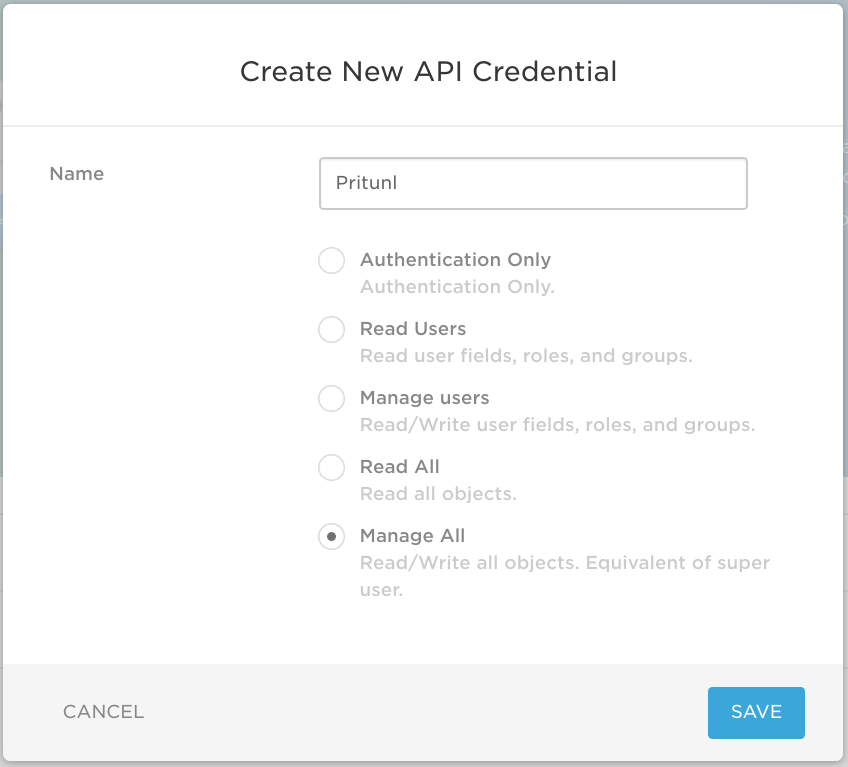
An API token can be used for secondary authentication using OneLogin Protect. This is not required if OneLogin Protect secondary authentication will not be used. To create a token click Settings then API and New Credential. Name the token Pritunl then select Manage All and save the token for later. The Manage All option is required for initiating push authentication requests.
Add Users to Pritunl App
After the OneLogin app has been created you will need to add users to the Pritunl app before they are able to use it. This can be done in the Users tab on the Pritunl app settings on OneLogin.
OneLogin App Id
Next get the OneLogin app ID from the url in the OneLogin application settings. The ID is the last number component of the URL. For example the ID for this url https://pritunl.onelogin.com/apps/581429/edit is 581429. This ID will be needed in the next step.
Configure Pritunl
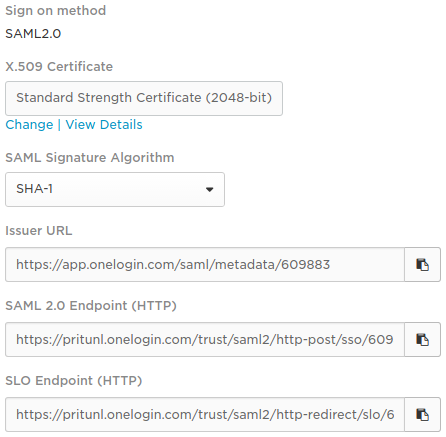
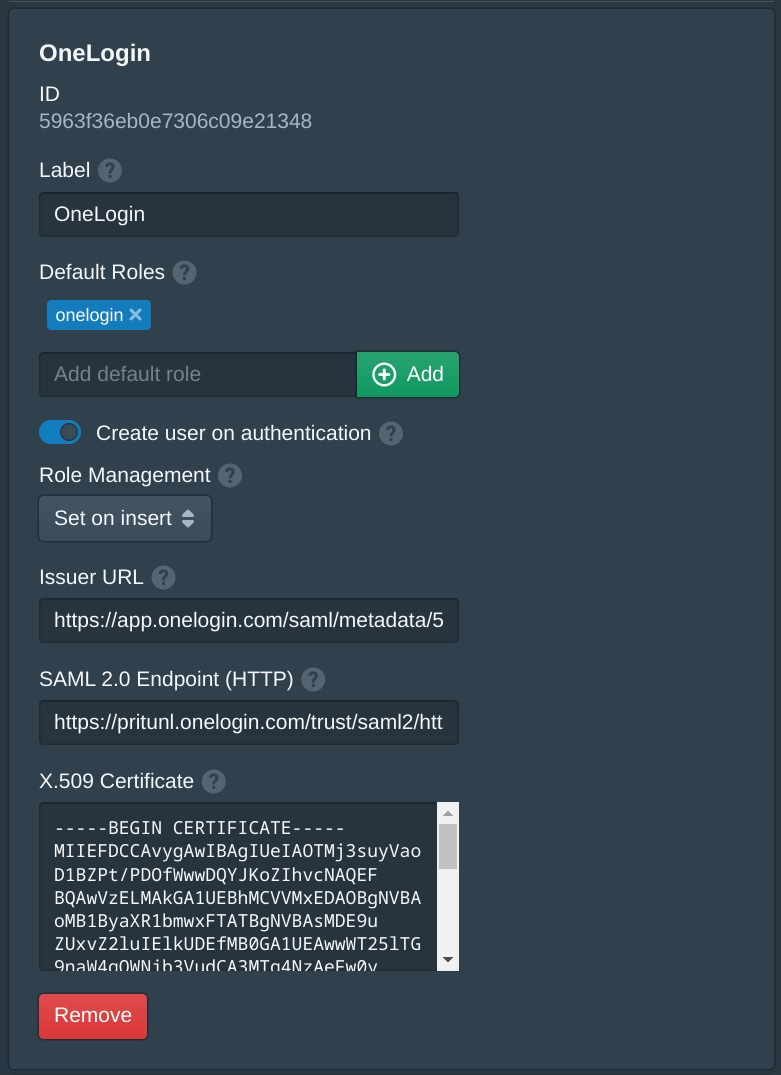
Once the OneLogin app has been configured click on the app then click Sign On and View Setup Instructions. In the Pritunl Zero settings tab select Okta and click Add Provider. Add any default roles that will apply to all users who authenticate with Okta. Copy the Issuer URL, SAML 2.0 Endpoint (HTTP) and X.509 Certificate from the OneLogin web console.
For Okta Push authentication add the Okta secondary provider on the right side. Set the Okta domain to the company Okta login domain. Then set the Okta API token. Write access on the token is required for push authentication. A policy will need to be created to apply the secondary authentication requirement to users.
Use the API token from earlier to fill in OneLogin API Client ID and OneLogin API Client Secret.
Updated 7 months ago
