JumpCloud
Single sign-on with JumpCloud
Although JumpCloud includes a pre-configured Pritunl application, this configuration was done incorrectly by JumpCloud and should not be used. Instead create a custom SAML application as shown below.
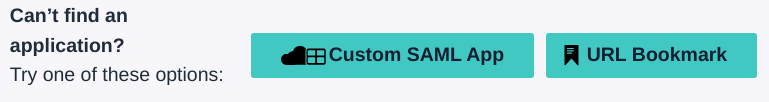
In the JumpCloud admin console click New Application then at the bottom click Custom SAML App.
Set the Display Name to Pritunl then open the SSO tab at the top.
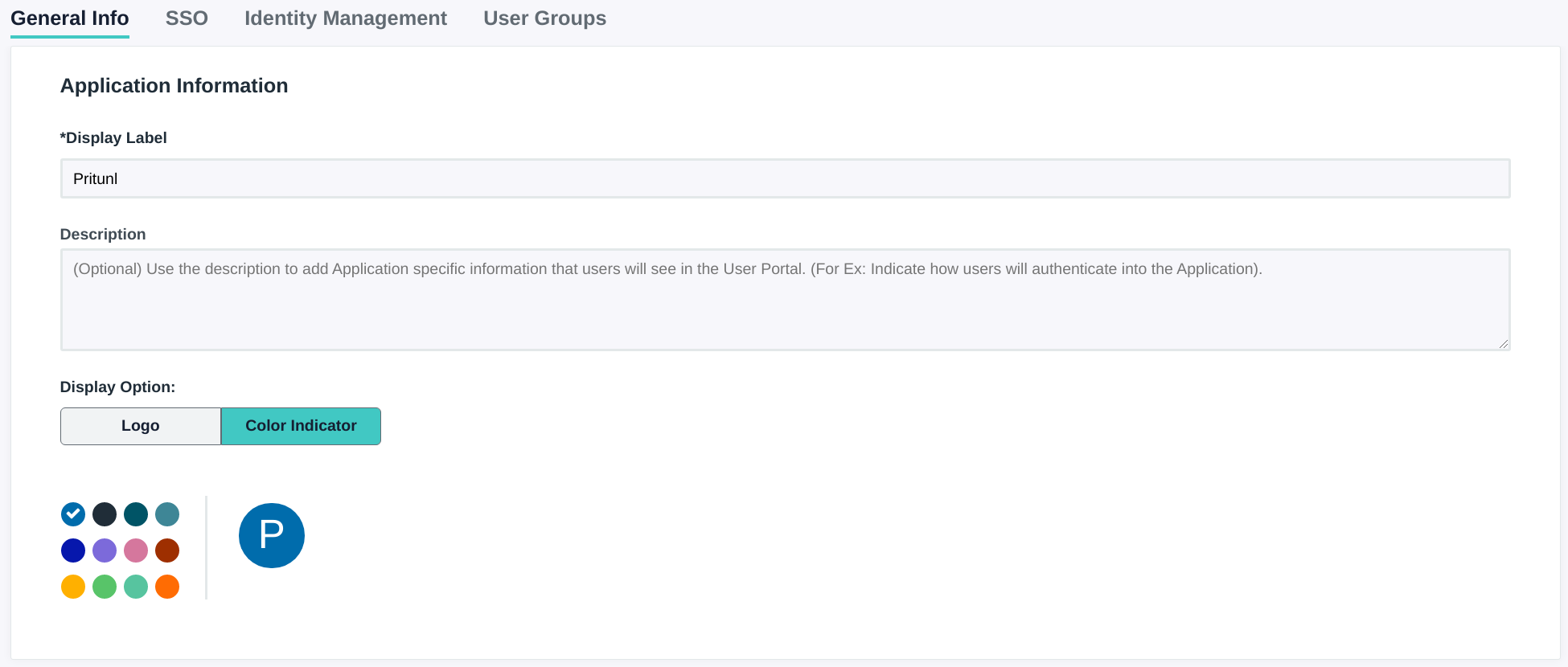
From the SSO tab scroll to the bottom and set IDP URL to pritunl followed by random numbers. This URL must be unique to other JumpCloud users. This URL will be needed in the next step.
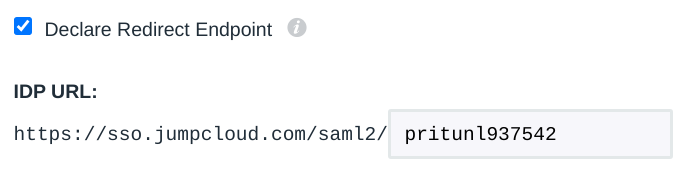
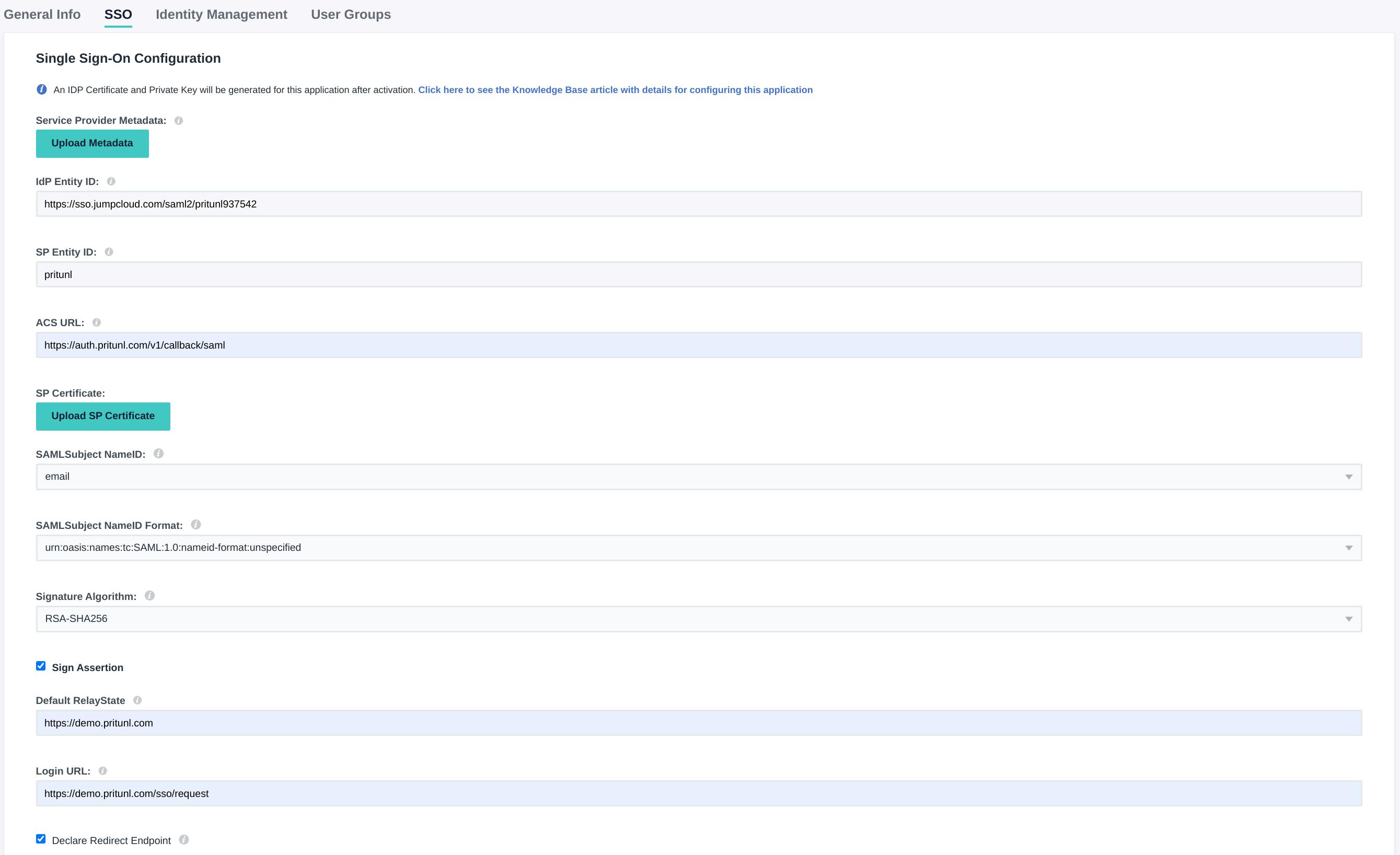
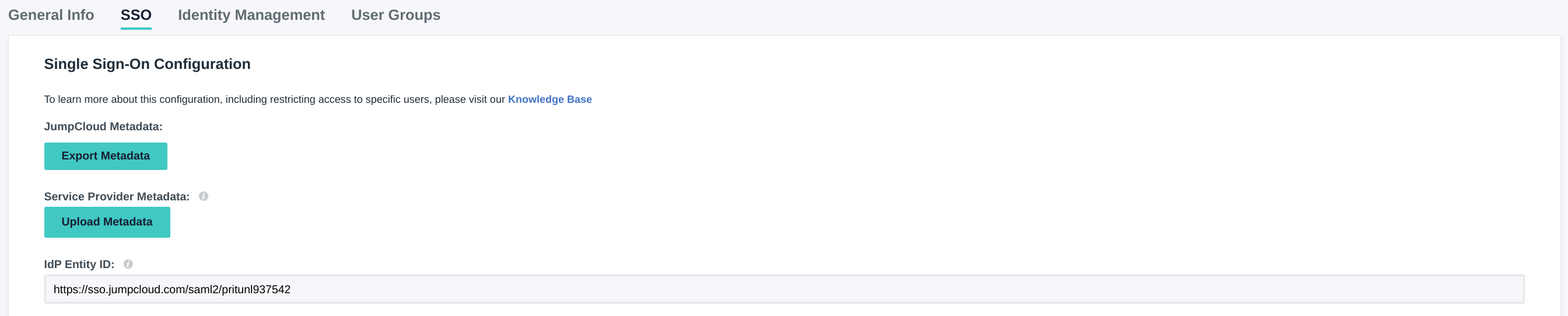
Set the IdP Entity ID to https://sso.jumpcloud.com/saml2/pritunl followed by the same numbers in the URL from the previous step. Then set the SP Entity ID to pritunl and the ACS URL to https://auth.pritunl.com/v1/callback/saml. Enable both Sign Assertion and Declare Redirect Endpoint. Then set the Default RelayState to the URL of your Pritunl server. Set the Login URL to the URL of your server with the path /sso/request
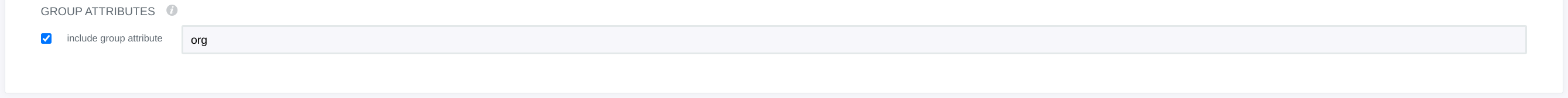
To map group names to organizations in Pritunl the JumpCloud group name must match an existing organization name in Pritunl. To use this feature enable include group attribute and set the value to org.
Once done click Activate then open the application page. In the SSO tab of the SAML application copy the URL in IdP Entity ID. This will be needed in the next steps. While on this page copy the app ID from the URL. In this example the page URL is https://console.jumpcloud.com/#/sso/61c44c96b87e5f50453473cf/details, the app ID in this URL is 61c44c96b87e5f50453473cf. This ID will be needed later.
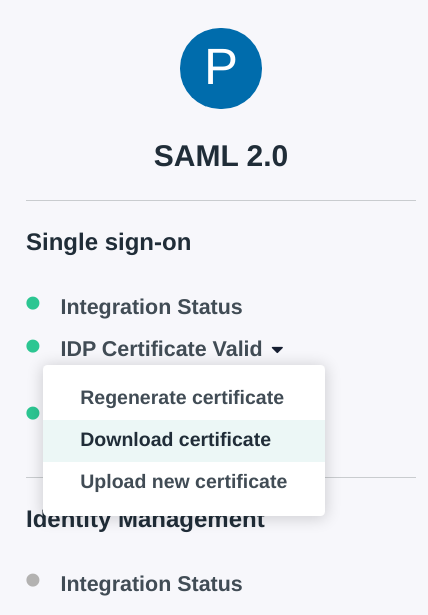
On the left side click IDP Certificate Valid then select Download certificate.
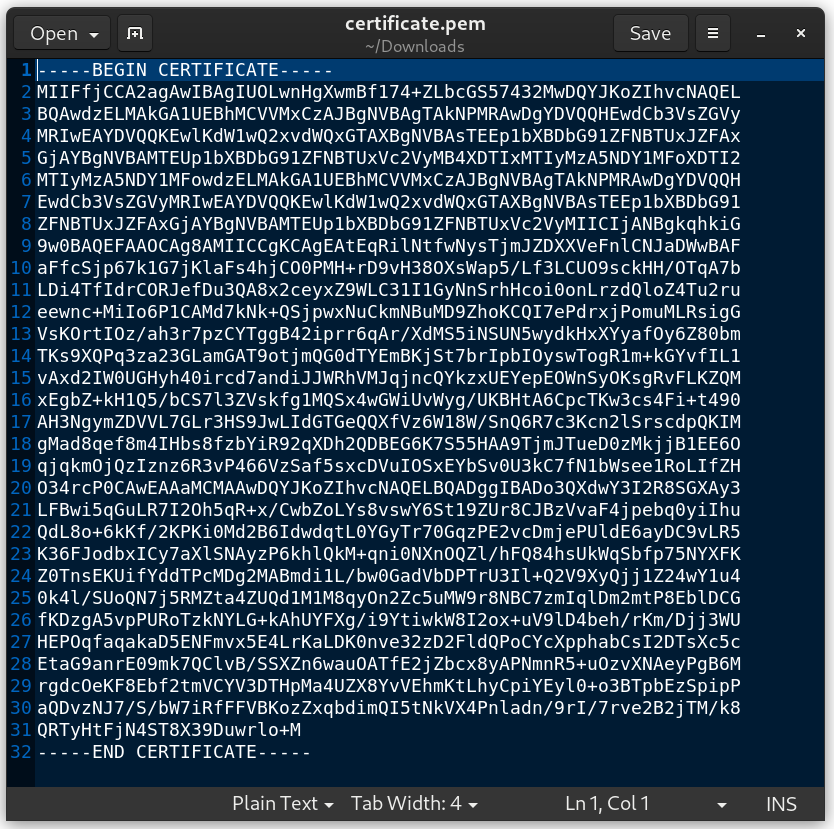
Open the downloaded certificate in a text editor to copy for the next steps.
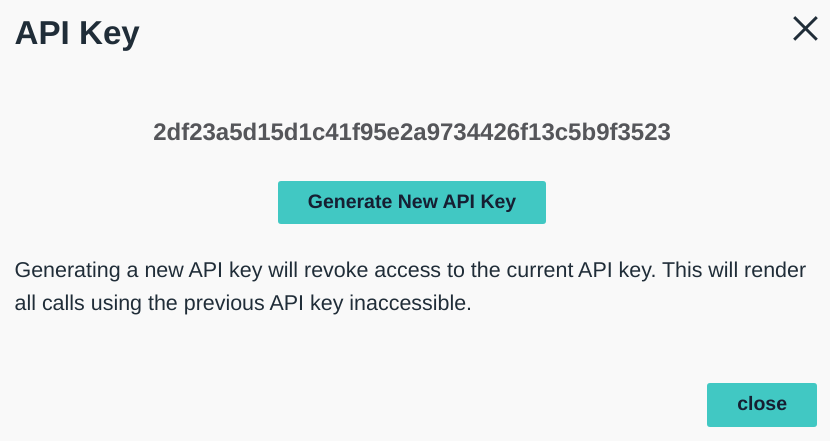
From the JumpCloud administrator console click the user icon in the top right then click API Settings.
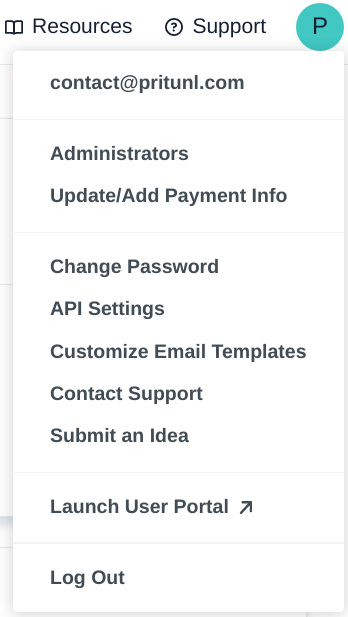
Copy this API key for the next step.
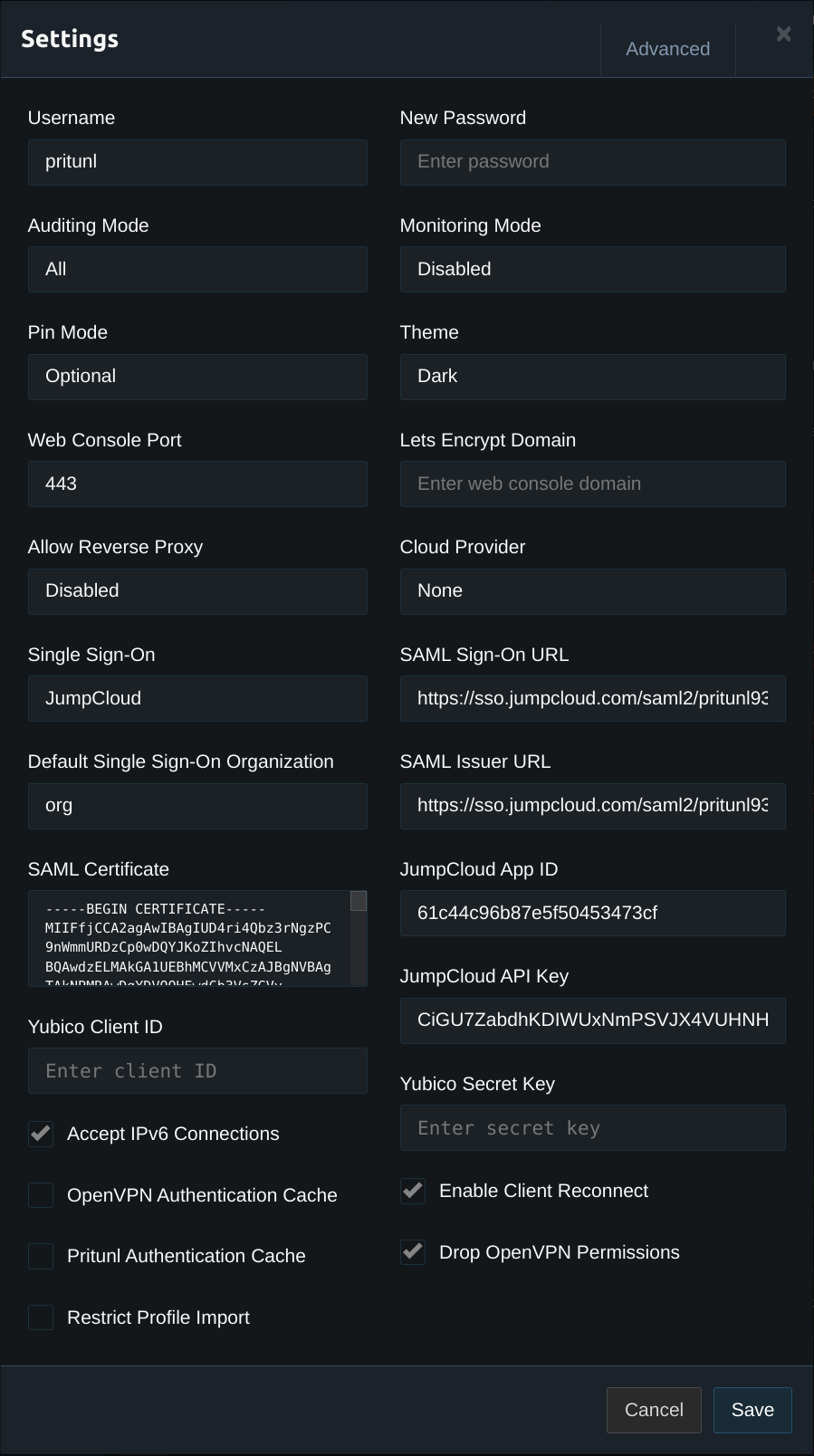
In the Pritunl web console click Settings. Set the SAML Sign-On URL and SAML Issuer URL to the IdP Entity ID from the previous steps. In this example https://sso.jumpcloud.com/saml2/pritunl is used. Copy the certificate downloaded in the previous steps to the SAML Certificate field. Set the JumpCloud App ID to the app ID from the URL in the previous step. Then set the JumpCloud API Key to the API key from the previous step.
Updated 7 months ago
