IPsec Router
Connect IPsec router to Pritunl Link
Extensive testing with different routers and cloud provider IPsec offerings has shown that these IPsec clients will significantly underperform an instance or server running IPsec. Running IPsec on a router should only be done when it is not possible to configure a pritunl-link client with port forwarding. Additionally many failover features will be unsupported when not using pritunl-link clients for IPsec.
Pritunl Link supports static hosts for connecting IPsec routers. This allows creating site-to-cloud configurations with any router that supports IPsec. Refer to Ubiquiti EdgeRouter Static or VyOS Static for guides specific to those routers. This guide will provide general information for other routers.
Static hosts are not able to automatically pull changes to the link configuration from the Pritunl server. Because of this the link configuration must be fully completed and all non-static hosts must be deployed first. The non-static hosts will push the public address of the host to the Pritunl server, this must be done before configuring the static host. If it's necessary to deploy a static host before non-static hosts the public address must be manually configured on the non-static hosts.
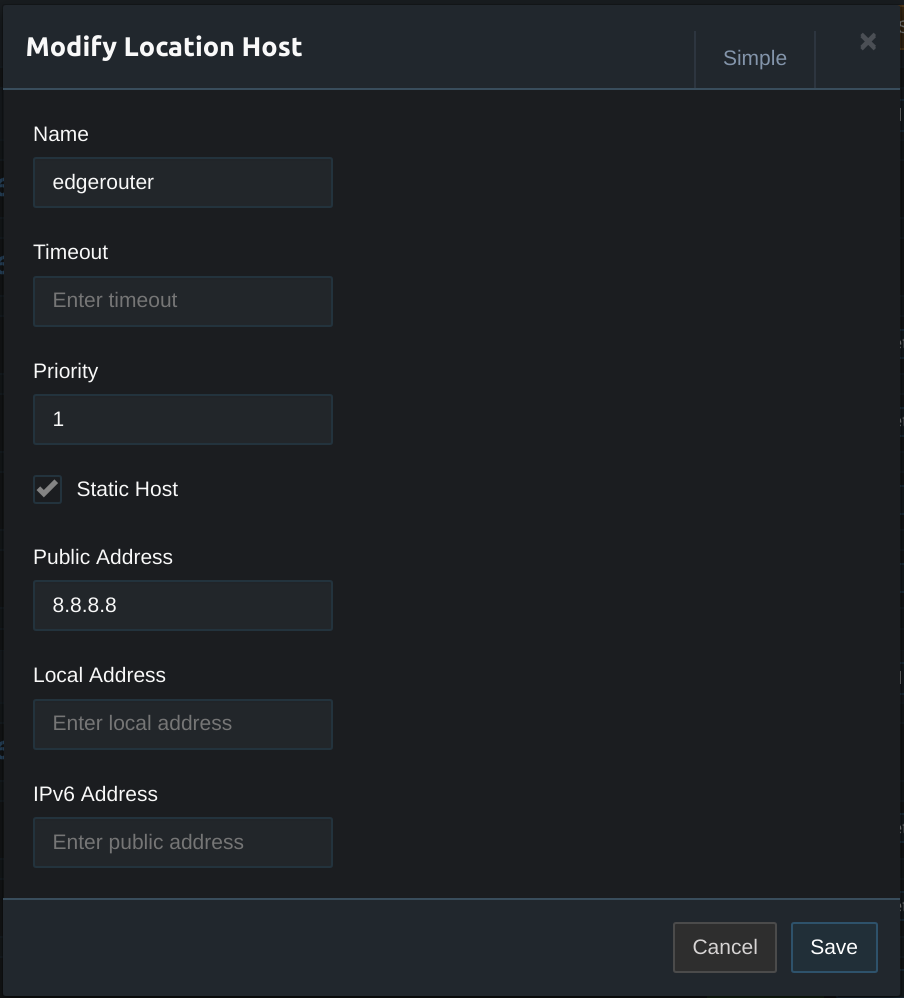
To configure a static host first create a location for the routers network and click Add Host in the location. Then click Advanced at the top right and enable Static Host. Set the Public Address to the public IP address of the EdgeRouter. If an IPv6 link is being configured also set the IPv6 Address.
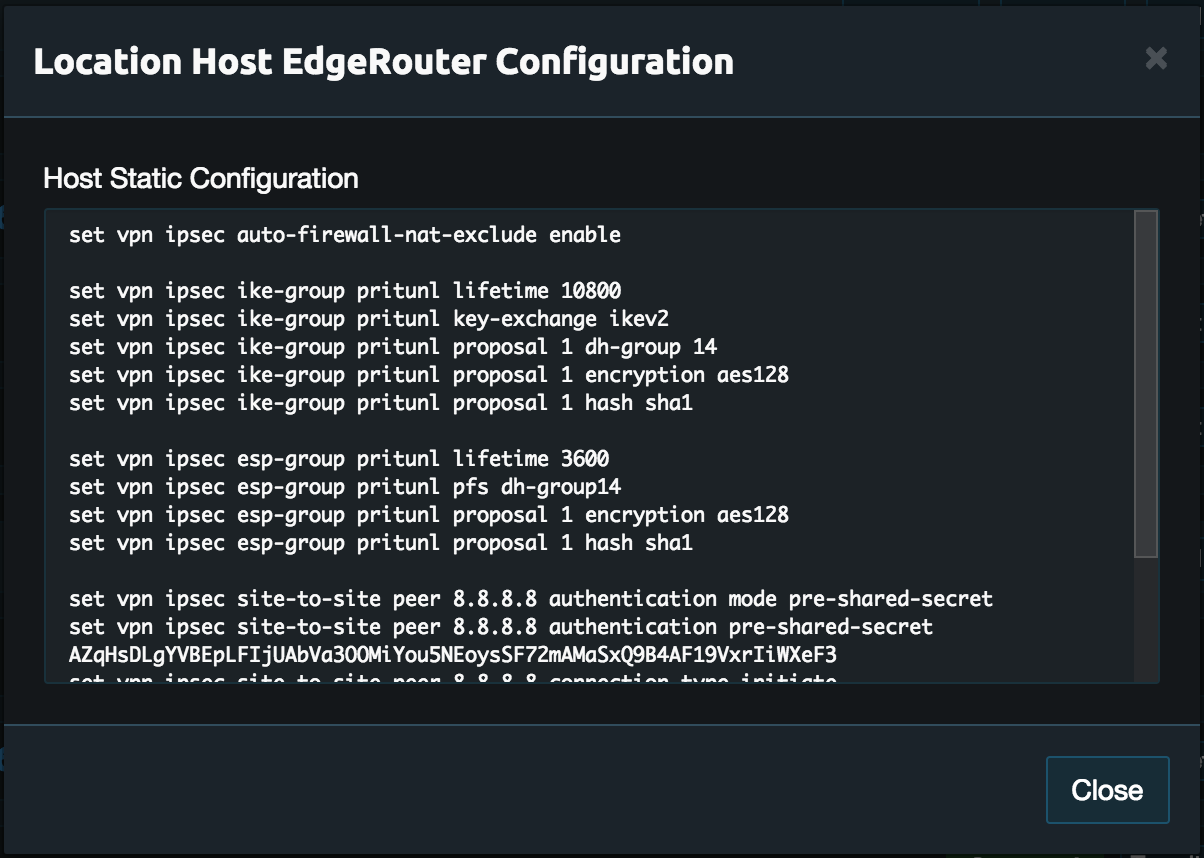
Once done a Get Conf button will be displayed on the right side of the host. Click this to get the IPsec configuration in a strongSwan ipsec.conf format. It may be easier to refer to the EdgeRouter format by clicking Get EdgeRouter Conf. Below is a list of encryption proposals supported by pritunl-link, use the first one that is available on the router.
aes128-sha256-modp2048s256 - AES-128, SHA-256, DH Group 24
aes128-sha256-ecp256 - AES-128, SHA-256, DH Group 19
aes128-sha256-modp3072 - AES-128, SHA-256, DH Group 15
aes128-sha256-modp2048 - AES-128, SHA-256, DH Group 14
aes128-sha256-modp1536 - AES-128, SHA-256, DH Group 5
aes128-sha1-modp2048s256 - AES-128, SHA1, DH Group 24
aes128-sha1-ecp256 - AES-128, SHA1, DH Group 19
aes128-sha1-modp3072 - AES-128, SHA1, DH Group 15
aes128-sha1-modp2048 - AES-128, SHA1, DH Group 14
aes128-sha1-modp1536 - AES-128, SHA1, DH Group 5
Once configured the other link locations should connect to the router.
Updated 7 months ago
